Indicators Of Attack (ioa)
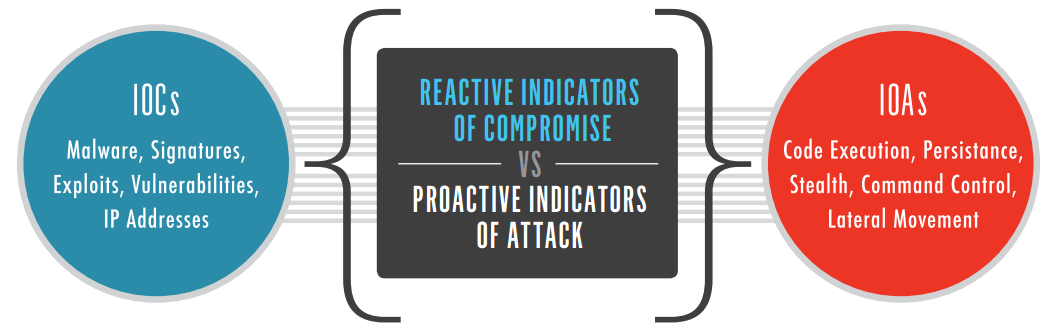
An IOC is a set of data about a malicious object or malicious activity. Just like AV signatures an IOC-based detection approach cannot detect the increasing threats from malware-free intrusions and.

Insight Provides Network Operation Centre 24 7 Which Helps The Clients And Customers By Protecting Them Network Operations Center Networking Data Security
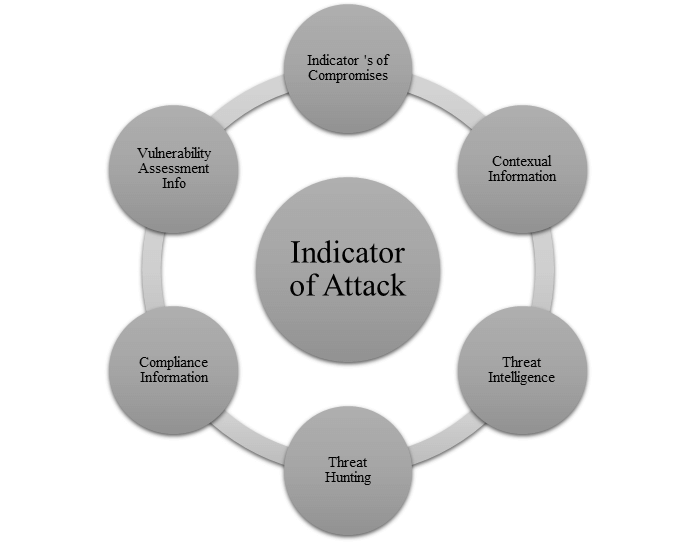
As per the experiences of threat hunting and threat intelligence professional Indicator of Attack is a collection of different IOC s to create true positive threat models.

Indicators of attack (ioa). Indicators of attack IoA are used to determine whether an attack is ongoing and must be contained before it can cause more damage. Dell last week released a. SafeBIOS Events IoA uses behavior-based threat detection at the BIOS level to.
Conversely although they are able to conduct after-the-fact investigations to uncover the markings of a compromise systems that detect IoAs work in real-time to detect exploits as they happen. Context-sensitive clues unlock early attack detection and action. When positioned properly within a more mature intelligence program IoAs can actually identify proactive identification and defensive strategies against new unknown threats.
In many ways it is a more strategic view of the TTPs of a threat actor or group. Kaspersky Anti Targeted Attack Platform uses IOC files conforming to the. Called Dell SafeBIOS Events Indicators of Attack IoA the utility gives organizations insights into whether their workers PCs are secure.
Kaspersky Anti Targeted Attack Platform uses two types of indicators for threat hunting. The SafeBIOS Events Indicators of Attack tool gives admins visibility into BIOS configuration changes and alerts them to potential threats. 10 Indicators of attack IoAs The following most common attack activities could have been used individually or in combination to diagnose an active attack.
Indicators of Attack IoA IoAs focus more on the WHY and intent of an actor. Internal hosts communicating to external hosts using non-standard ports or. Internal hosts communicating with known bad destinations or to a foreign.
Kaspersky Anti Targeted Attack Platform uses IOC files conforming to the. Sequence of events or exploits that an adversary must conduct in order to succeed. 2 Internal hosts with non-standard ports.
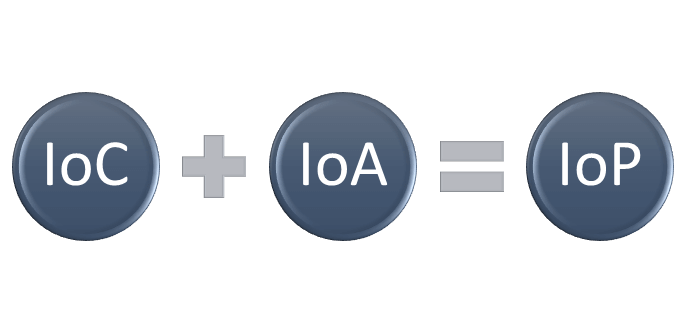
1 Internal hosts with bad destinations Internal hosts communicating with known bad destinations or to a foreign country where you dont conduct business. 1 Indicators of Attack IoA Indicators of Attack IoA An IoA is a unique construction of unknown attributes IoCs and contextual information including organizational intelligence and risk into a dynamic situational picture that guides response. Both IoC and IoA work with evidence and metadata that give investigators clues into the state of an attack.
Managing indicators of compromise and attack Kaspersky Anti Targeted Attack Platform uses two types of indicators for threat hunting. Examples of IOA include Use case of Indicators of Attack. What are the Indicators of Attack IoA According to McAfee a cybersecurity firm the IoA is a unique construction of the unknown attributes IoC and contextual information including organizational risk and intelligence into a dynamic situational picture.
10 Indicators of attack IoAs 1 Internal hosts with bad destinations. IoCs are used after an attack was contained when the organization needs to know where what and how. An IOC is a set of data about a malicious object or malicious activity.
10 Indicators of attack IoAs The following most common attack activities could have been used individually or in combination to diagnose active attacks. Recording and gathering Indicators of Attack IOA and analyzing them enables your team to view activity in real time and react in the present and provides first responders with the tools necessary to instantly reconstruct the crime scene or even intervene while an attack is still in progress. IOC Indicator of Compromise and IOA Indicator of Attack.
3 Public ServersDMZ to. IOC Indicator of Compromise and IOA Indicator of Attack. In response Dell Technologies is introducing Dell SafeBIOS Events Indicators of Attack IoA to further protect our commercial PCs which are already the most secure in the industry.
1 Internal hosts with bad destinations Internal hosts communicating with known bad destinations or to a foreign country where you dont conduct business. Indicators of attack IOA focus on detecting the intent of what an attacker is trying to accomplish regardless of the malware or exploit used in an attack.
The Importance And Difference Of Ioc And Ioa Logsign
Indicator Of Attack Vs Indicator Of Compromises Indicator Of Pivot

Indicators Of Attack Ioa Explained Video Crowdstrike Uk

What Are Indicators Of Attack Ioa

Blue Ocean Strategy Summary And Examples Blue Ocean Strategy Blue Ocean Red Ocean

Pin On Poc Network Tech Updates

Indicator Of Attack Vs Indicator Of Compromises Indicator Of Pivot

A New Cryptoshield Ransomware Being Distributed Via Eitest Campaign Kindergarten Skills Kindergarten Worksheets Spelling Worksheets

Patterns Of Attack You Re Looking For Answers Not Just Indicators Vmware Carbon Black

What Are Indicators Of Attack Ioa

Threat Detection Indicator Of Attack Vs Indicator Of Compromise

Kaspersky Lab Discovered A New Sophisticated Shamoon Linked Malware Dubbed Stonedrill Malware Kaspersky Lab Cyber Security

Threat Detection Indicator Of Attack Vs Indicator Of Compromise

Indicator Of Attack Ioa S And Activities Soc Siem How To Memorize Things Cyber Security Event Management

It Managed Services By Us Technosoft Network Operations Center Infrastructure Management Services Networking
Indicator Of Attack Vs Indicator Of Compromises Indicator Of Pivot

Indicator Of Attack Vs Indicator Of Compromises Indicator Of Pivot


Post a Comment for "Indicators Of Attack (ioa)"